Pegasus spyware: FBI vows not to use after grilling from Capitol Hill
The FBI insisted it never planned to use the program to trhttps://www.foxnews.com/ack Americans
The FBI has come under scrutiny in recent months after it purchased a license to use the highly effective spyware program. FBI officials have insisted they did not end up using the program and had intended to only use it for research. Nevertheless, internal documents suggest they had plans to expand its use–including for tracking Americans. The FBI now tells Fox News it will drop the program.
Director Wray faced a grilling from members of Congress on the issue in hearings earlier this year, when he stated that his organization had never used to program.

“The Director’s testimony was accurate when given and remains true today – there has been no operational use of the NSO product to support any FBI investigation,” the FBI told Fox.
Sen. Ron Wyden, D-OR, accused Wray of essentially lying – or at least fudging the truth – in testimony earlier this year. Wray was asked about the FBI’s purchase of the spyware and bureau plans to use it in criminal investigations, including tracking Americans. Wray insisted the FBI would only use Pegasus for “research,” but the New York Times soon obtained internal FBI documents indicating this was not accurate – the FBI had hoped to use Pegasus more broadly.
Wray was asked about the FBI’s purchase of the spyware and bureau plans to use it in criminal investigations, including tracking Americans. Wray insisted the FBI would only use Pegasus for “research,” but the New York Times soon obtained internal FBI documents indicating this was not accurate – the FBI had hoped to use Pegasus more broadly.
 Pegasus has already proven capable of infiltrating the phones of U.S. officials working overseas, something Rep. Adam Schiff, D-Calif., highlighted in a spyware hearing this summer.
Pegasus has already proven capable of infiltrating the phones of U.S. officials working overseas, something Rep. Adam Schiff, D-Calif., highlighted in a spyware hearing this summer.
“Late last year, multiple news organizations reported that mobile phones used by U.S. diplomats in Uganda had been compromised by NASA’s Pegasus tool,” Schiff said at the time. “It is my belief that we are very likely looking at the tip of the iceberg and that other U.S. government personnel have had their devices compromised, whether by a nation state using NSA services or tools offered by one of its lesser known but equally potent competitors.”

Experts say the spyware has legitimate uses but is also a powerful tool for authoritarian governments. Mexico used Pegasus in its effort to track down El Chapo, and Saudi Arabia also used it to track journalist Jamal Khashoggi prior to orchestrating his murder, according to cyber defense expert Jason Blessing.
The Spy Factories: NSA’s XKeyscore Isn’t the Only Program Tracking You
When whistleblower Edward Snowden revealed his NSA files in 2013, one sneaky program stood out: XKeyscore, a secret system that spies can use to search and analyze nearly everything you do on the internet in real-time.
XKeyscore is still hoovering up your internet searches, passwords, user names, emails, and personal messages a decade later. In fact, it’s not the only tool governments used to spy on your personal data. Here are five ways the US, Britain, Israel, Canada, and others may be spying on you right now.

CIA snooping on Americans
The CIA is vacuuming up data in bulk so spies can sift through it, according to two members of the US Senate Intelligence Committee.
If the data collection happens overseas or falls into a statutory black hole, it comes under Executive Order 12333 which means there’s little oversight. “What stops the CIA from poring through the data looking for Americans’ information? Let’s be honest: nothing,” according to the Brennan Center for Justice.
Senator Ron Wyden said he is also concerned the US Defense Intelligence Agency is buying consumer smartphone location data from a third-party broker and the Department of Homeland Security is helping to compile money transfer records.

Pegasus software
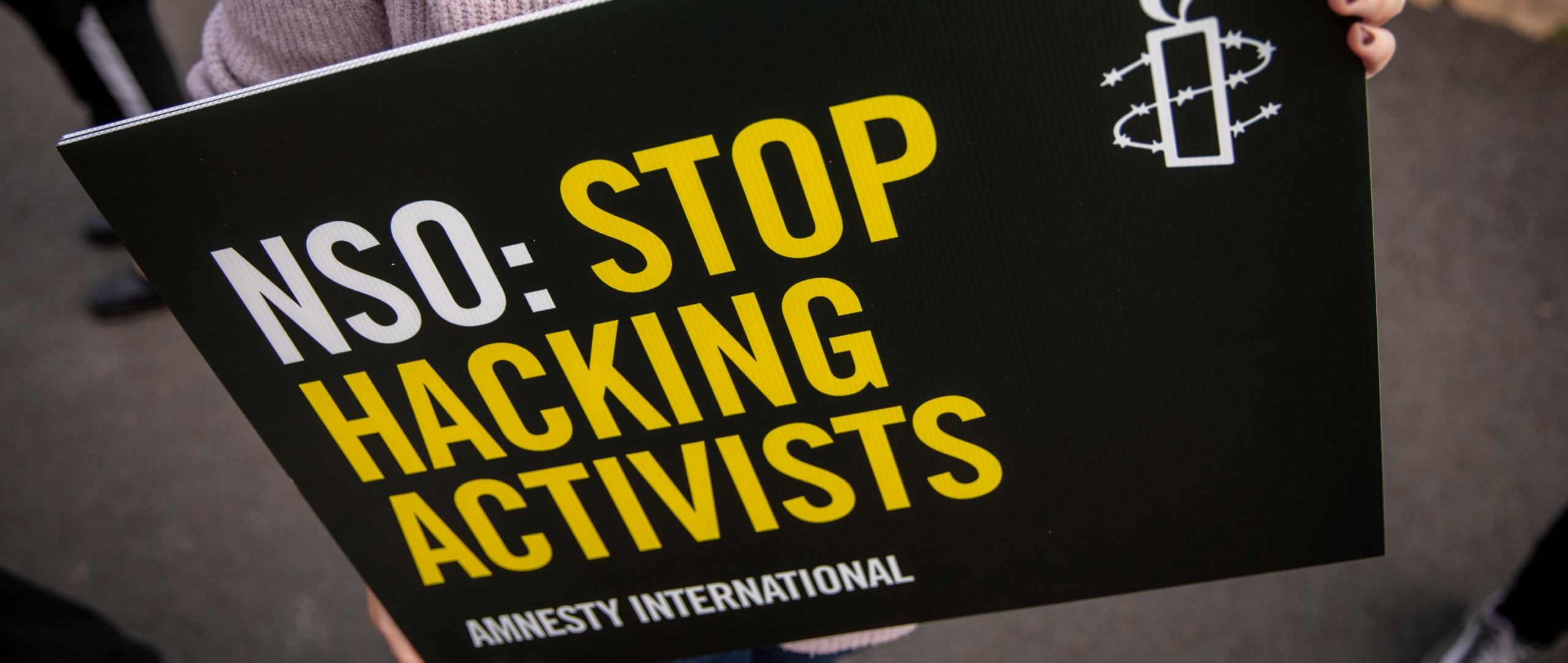
The Israeli company NSO Group developed Pegasus spyware to target terrorists but governments have used it to track at least 180 journalists, political dissidents, activists, and heads of state including French President Emmanuel Macron.
More than 50,000 phone numbers targeted for surveillance by Pegasus’ customers were leaked to Amnesty International, revealing a massive global privacy breach. Once installed, the software operator can receive text messages, contact lists, and calendar events, and can turn on the phone’s camera and microphone to capture activity in the phone’s vicinity.
Who uses it? The FBI ‘tested’ Pegasus spyware but said they haven’t used it in investigations. Canada’s CitizenLab linked Pegasus to operations in 45 countries including Mexico, Bahrain, Kazakhstan, Morocco, Saudi Arabia, and the UAE. Israeli police used the spyware to scrutinize citizens’ phones. The son of ex-Israeli PM Benjamin Netanyahu was one such target. Not all countries have access to Pegasus software. Israel reportedly blocked Ukraine from buying a license, fearing Russia would be angry if Pegasus was sold to a regional foe.

Codename Tempora: Britain’s GCHQ cyberspies
The European Court of Human Rights ruled in 2021 that GCHQ spies were acting unlawfully when they intercepted online communications in bulk. Judges also criticized GCHQ’s regime for sharing sensitive digital intelligence with foreign governments.
The data included information from passports, travel records, financial data, telephone calls, emails, and open or covert sources.
The court case revealed that Britain’s spies had secretly collected bulk personal data since the late 1990s and gathered information on people ‘unlikely to be of intelligence or security interest’. UK lawyers argued that the information was needed for national security.

Vault 7: CIA hacking techniques
In 2017, WikiLeaks published what it described as thousands of pages of internal CIA discussions about Agency hacking techniques. CIA spies could apparently access Apple iPhones, Google Android devices, and other gadgets to capture text and voice messages before they were encrypted with software.
By the end of 2016, the CIA’s Center for Cyber Intelligence had more than 5,000 registered users and produced more than 1,000 hacking systems, trojans, viruses, and other ‘weaponized’ malware, creating, in effect, its own NSA with less accountability, according to WikiLeaks.
The House Intelligence committee was ‘looking into the report’ by Yahoo! News in 2021 that claimed the CIA allegedly plotted revenge for the WikiLeaks revelations by targeting founder Julian Assange.

CSIS: Canada’s spies creep forward
Canada’s CSE – the signals intelligence group that collects data much like the NSA does in the US – received new powers in 2019 under a law designed to crack down on terrorists. Privacy advocates worry the law is an invitation for mass surveillance and see potential problems.
Critics have long complained about CSE which, in 2012, spied on Canadians using public WiFi networks in Canadian airports. The agency – and its watchdog – argued that they were only collecting metadata (for example, an IP or email address and phone number) rather than the content of messages.
“But we (and they) know that metadata can reveal tons of private information about a person and their life: where they have been, what they believe, who they talk to, etc,” according to Canada’s International Civil Liberties Monitoring Group.
- NSA-backdoored equipment info found OFF this website
- U.S. Government Catalogue of Cellphone Surveillance Devices
- Backdoors on Wikipedia
- National Security Agency
- Central Intelligence Agency
- NSA EXTRACTED INFO
- CRYPTO MUSEUM
- Edward Snowden
- Stingray
- Pegasus Spyware
- X-Keyscore